API Security: How to avoid Broken Object Level Authorization & Broken Function Level Authorization | by Sagara Gunathunga | Medium

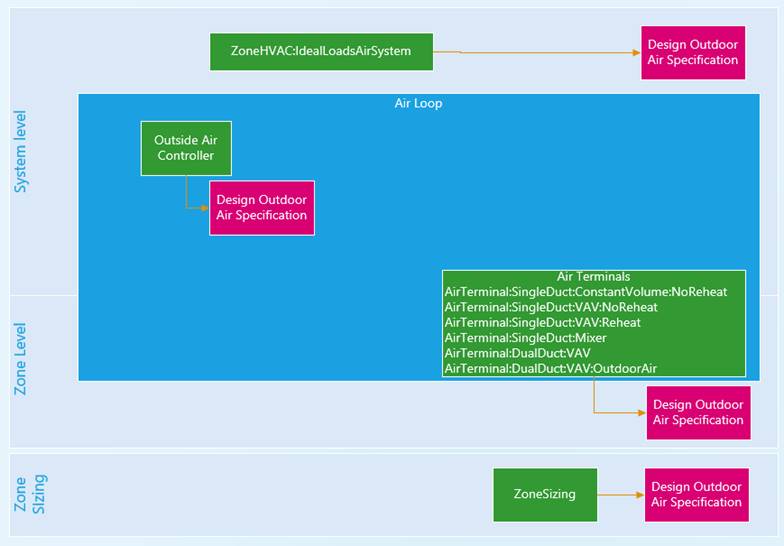
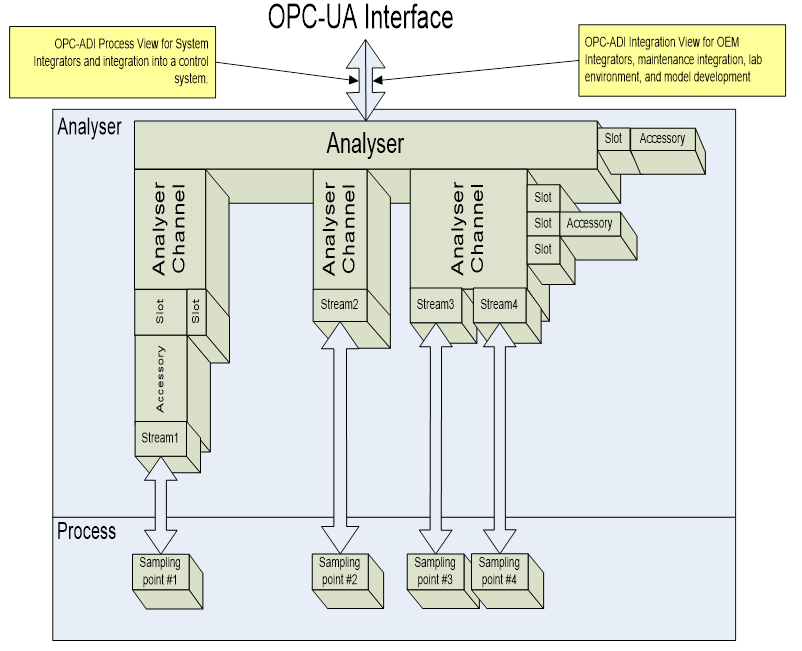
System-level architecture for building automation systems: Object-orientated design and simulation | Semantic Scholar
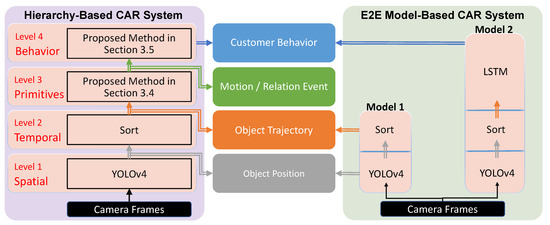
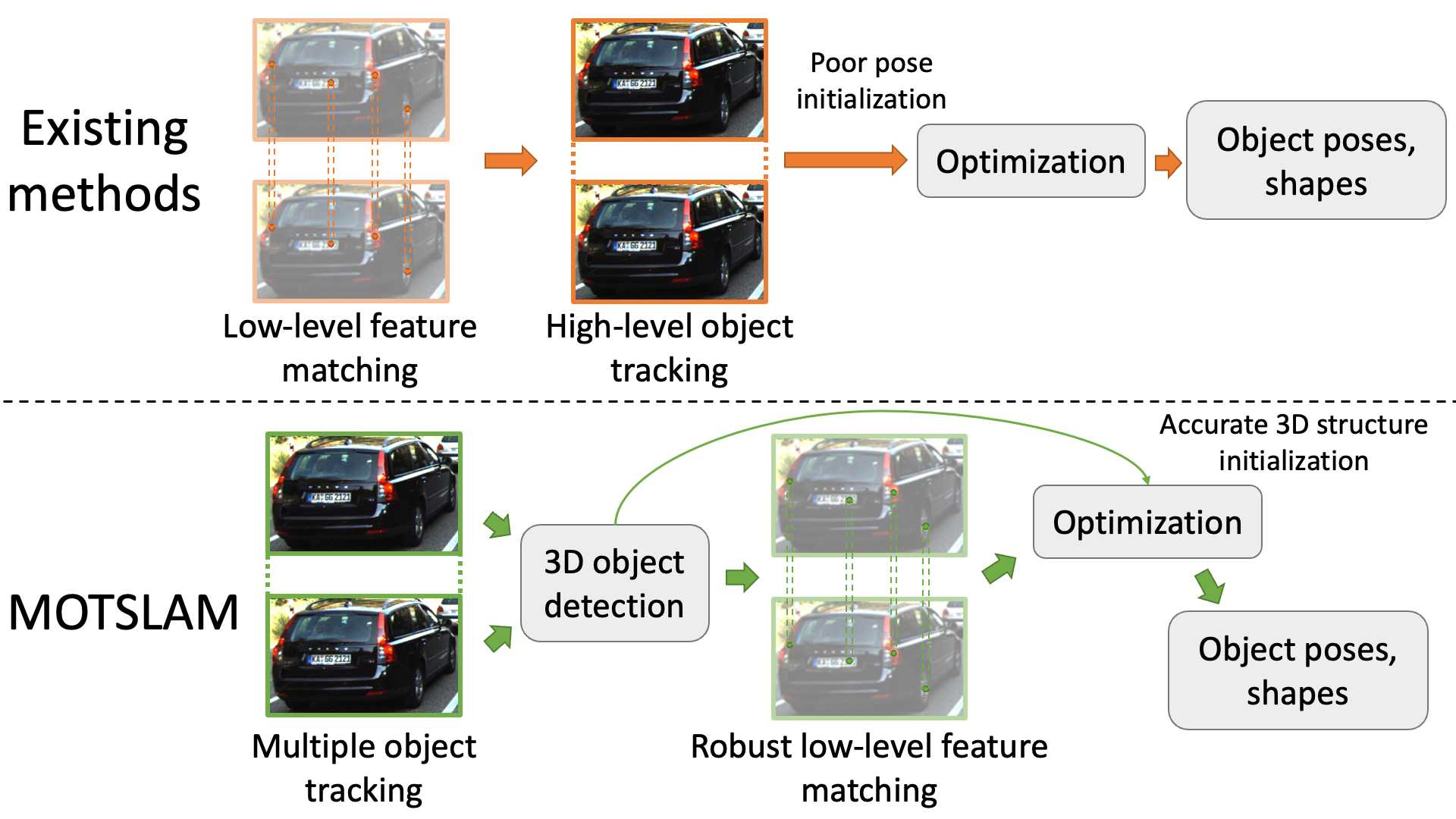
Sensors | Free Full-Text | A Hierarchy-Based System for Recognizing Customer Activity in Retail Environments

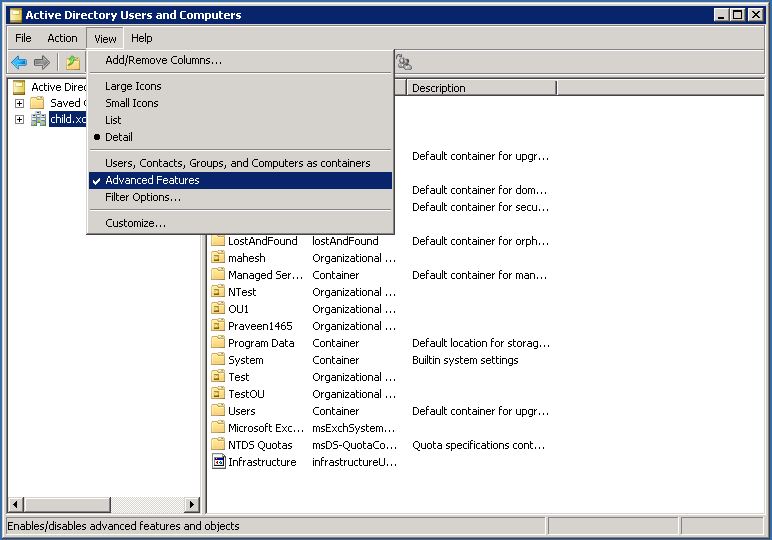
GTU MCA MATERIAL FOR DBMS II: Difference Between System Level Privileges and Objects Level Privileges
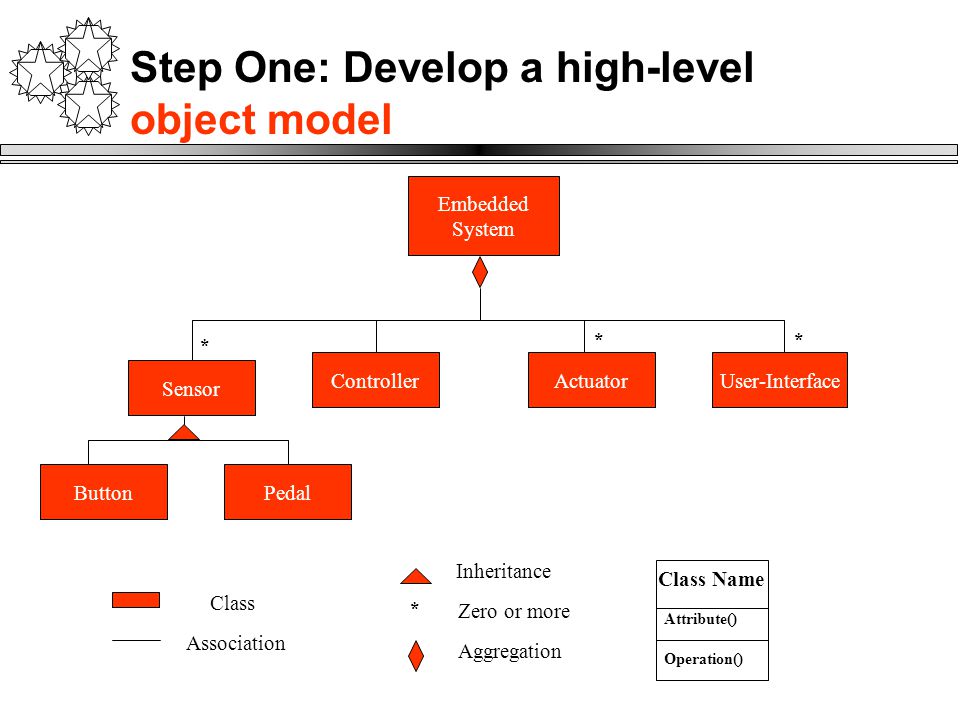
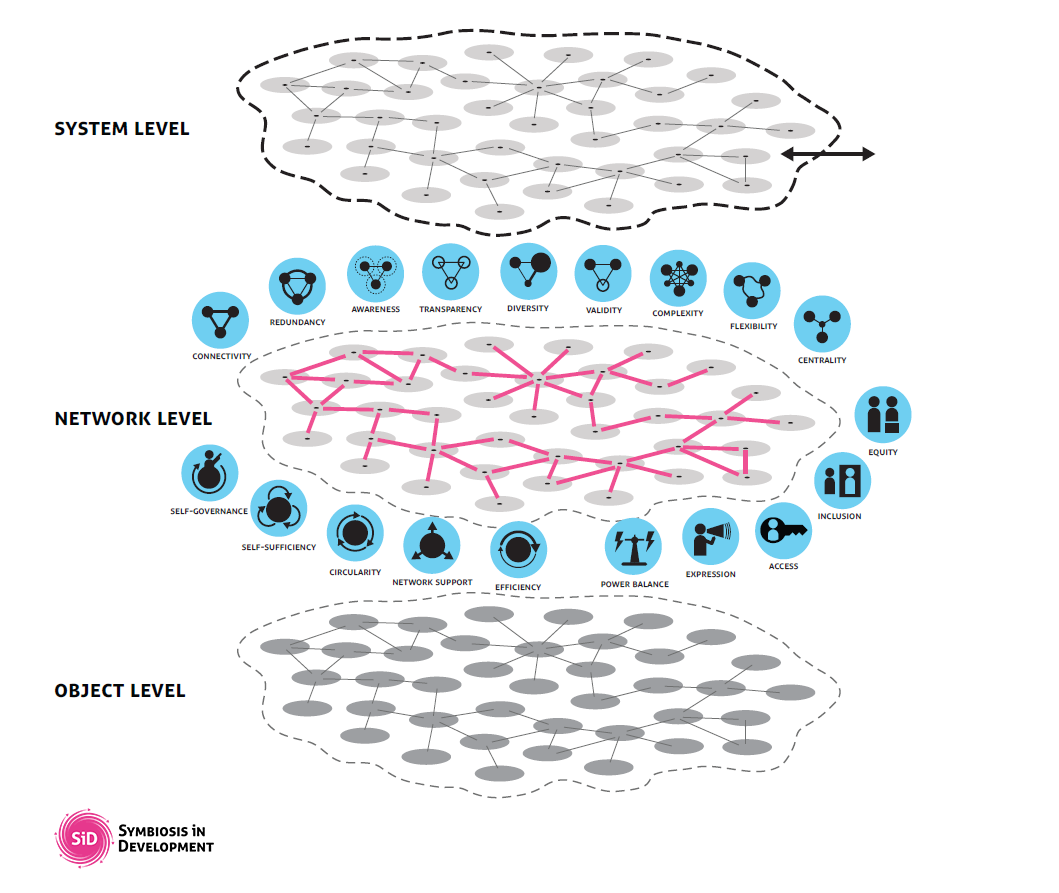
Embedded Systems Details. Object Model: Four main system objects or classes Controller object might be made up of several controllers is the brains of. - ppt download

Sensors | Free Full-Text | A Hierarchy-Based System for Recognizing Customer Activity in Retail Environments