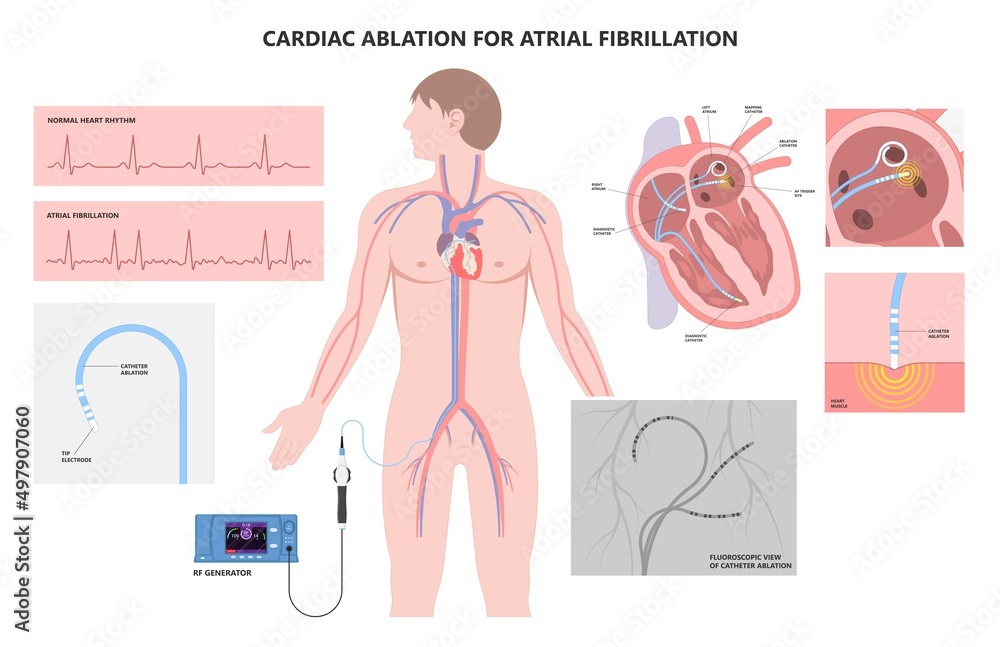
Vecteur Stock Cardiac catheter ablation treatment Atrial fibrillation rhythm problem minimally invasive procedure attack cath lab treat Coronary x-ray Radio frequency Sinus Ventricular SVT ECG ICD Radiofrequency AV | Adobe Stock
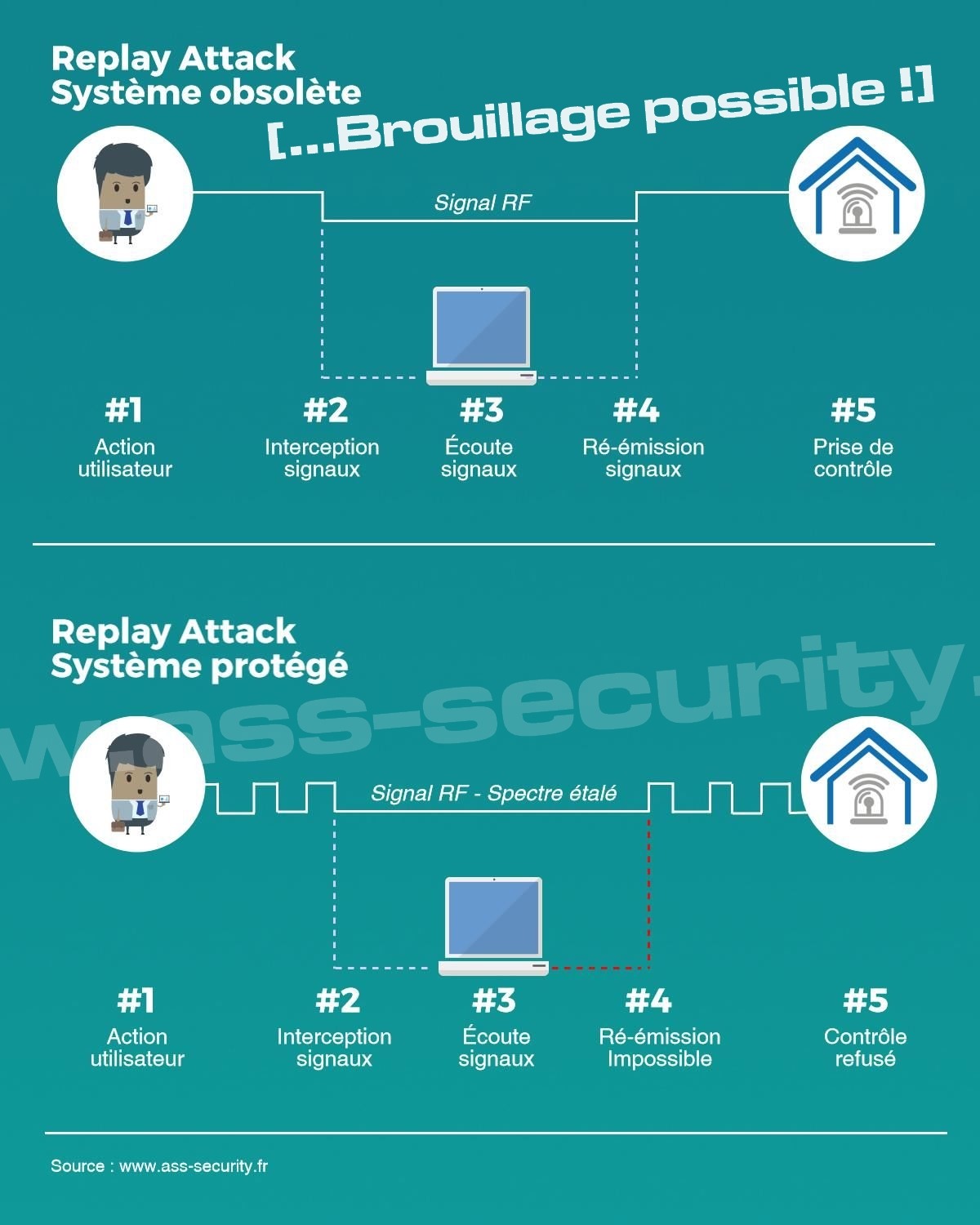
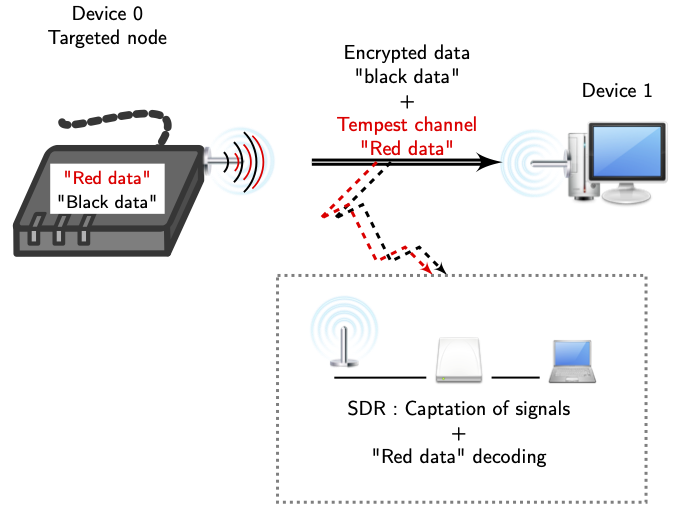
Dossier : Alarme sans-fil, Brouillage, Piratage d'une alarme Radio, Vulnérabilités, Perturbations...

Radio Frequency: An Airbone Threat to Corporate and Government Networks | 2020-07-06 | Security Magazine

U.S. review finds directed radio frequency attack likely culprit in diplomats' illnesses in Cuba | National Post
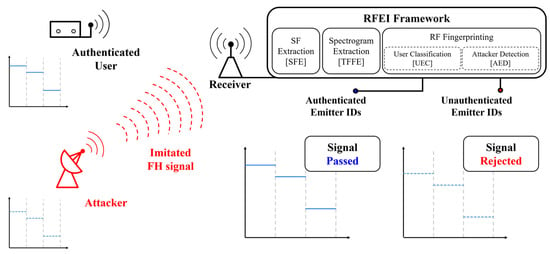
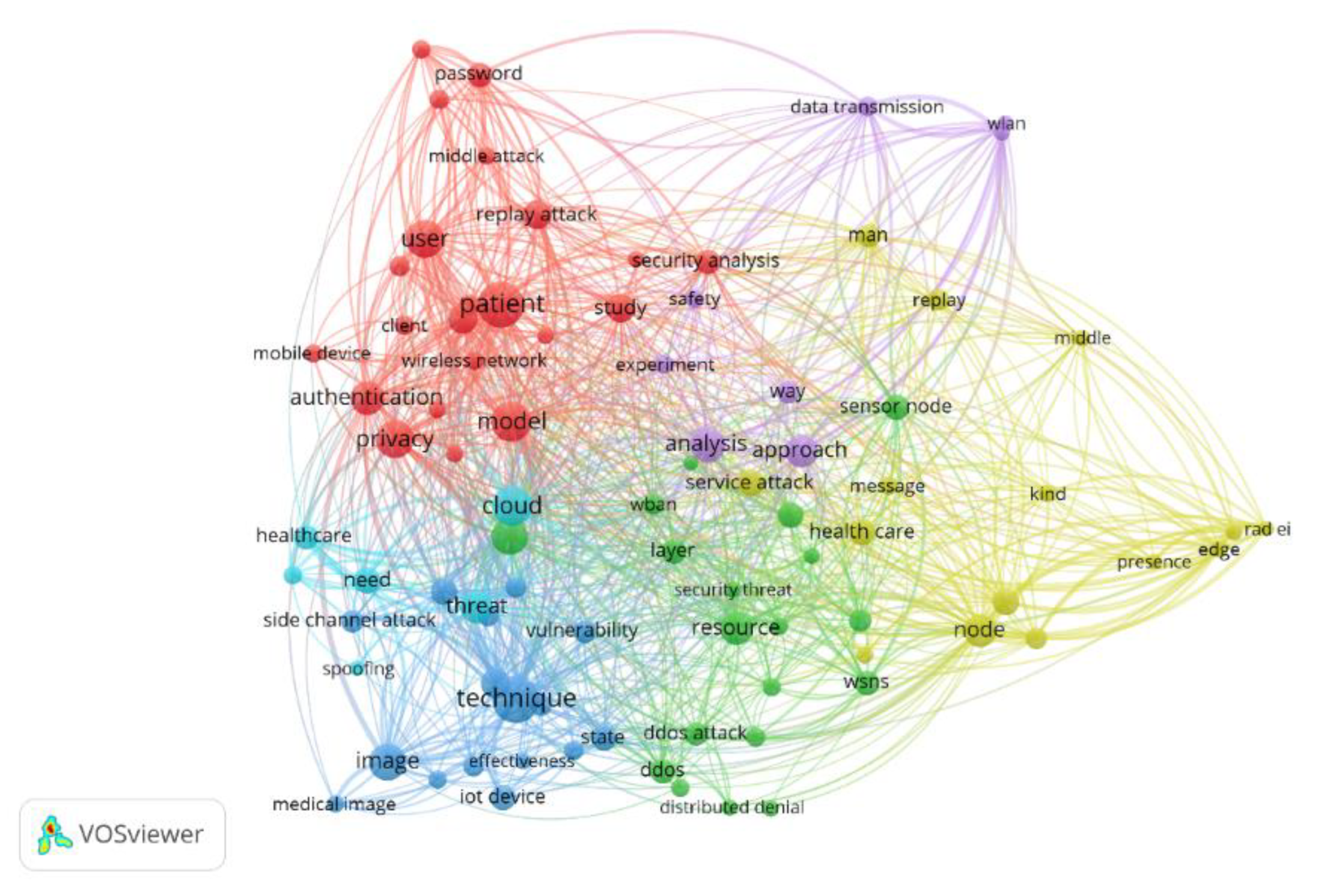
Applied Sciences | Free Full-Text | Radio Frequency Fingerprinting for Frequency Hopping Emitter Identification









_637280703542341277.png)