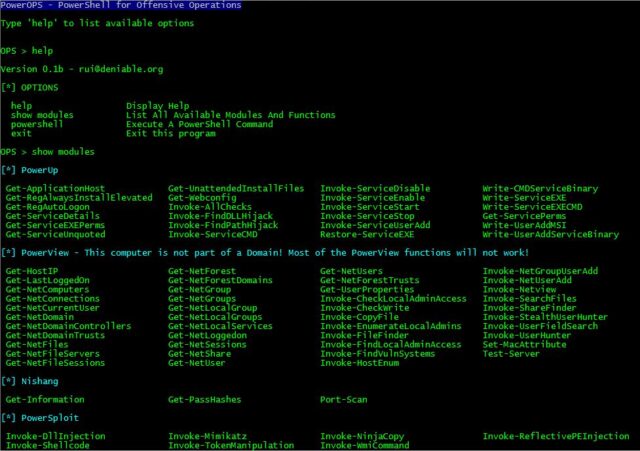
PowerOPS - PowerShell Runspace Portable Post Exploitation Tool - Darknet - Hacking Tools, Hacker News & Cyber Security

Post-Exploitation Techniques: Maintaining Access, Escalating Privileges, Gathering Credentials, Covering Tracks | Black Hat Ethical Hacking
WMEye - A Post Exploitation Tool That Uses WMI Event Filter And MSBuild Execution For Lateral Movement

Evasor - A Tool To Be Used In Post Exploitation Phase For Blue And Red Teams To Bypass APPLICATIONCONTROL Policies

Florian Roth on X: "mimikittenz post-exploitation powershell tool that extracts plain-text passwords from memory https://t.co/wyIpJH4gWV https://t.co/L2Gi2uN0YV" / X

Post Exploitation Tool | Windows hacking tool explained | RDP for any windows | #RedTeam | Pen Test - YouTube